












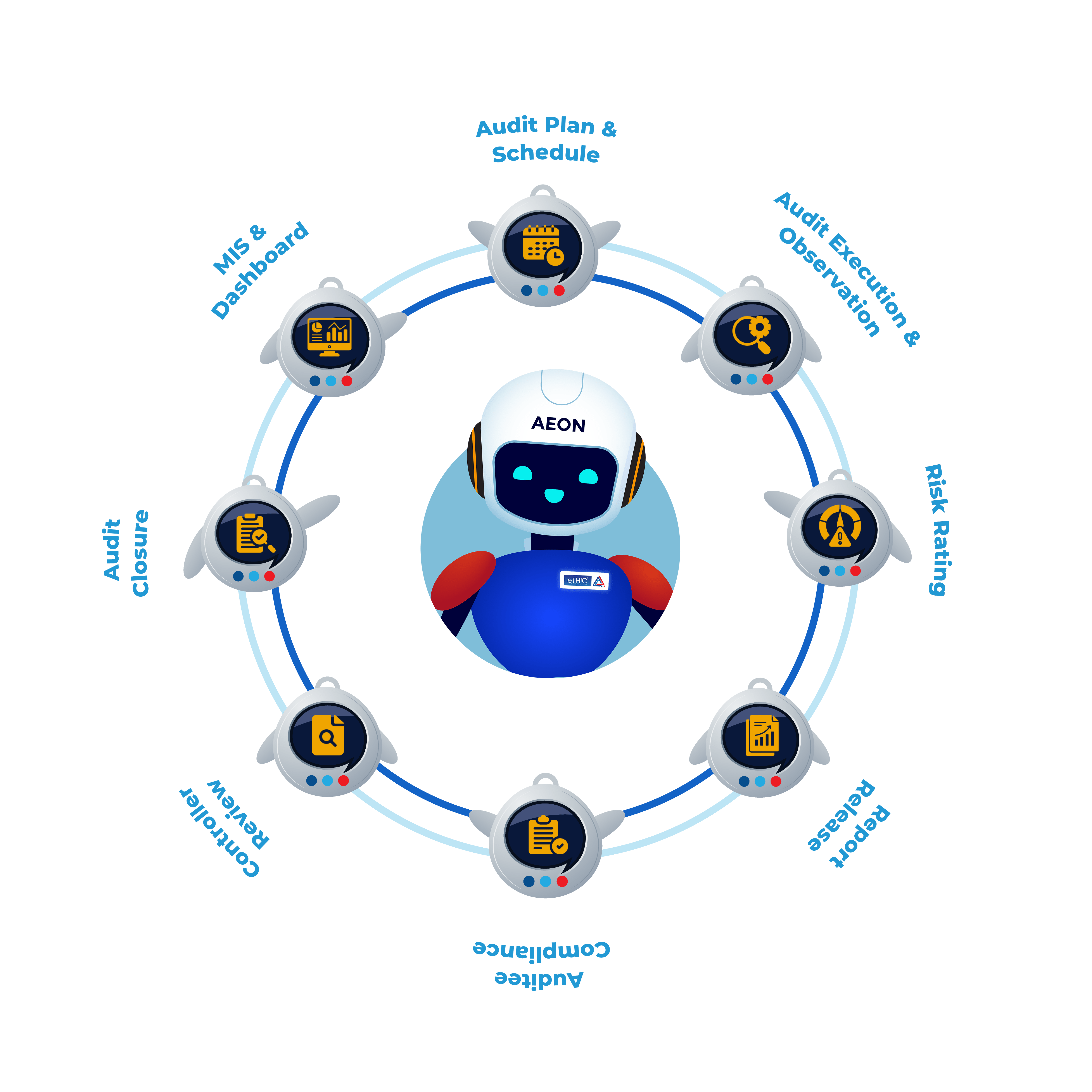
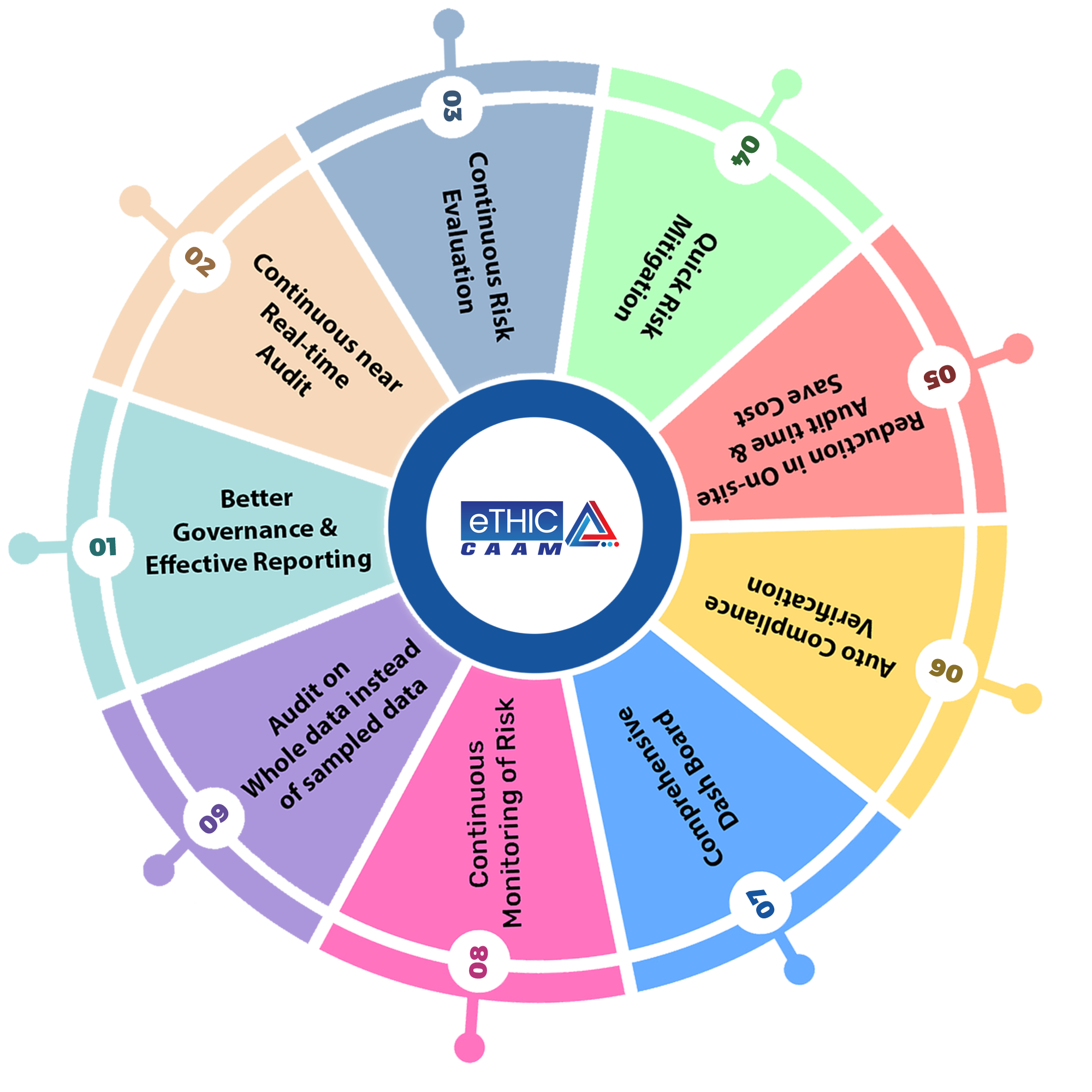
A digital solution for continuous Audit automation and monitoring is eTHIC CAAM, a customized system. The benefits of digitalized continuous Audits include improved Risk management inside the organization and the ability to quickly discover deviations and noncompliance.
Risk is regularly evaluated, which improves Governance, reduces Audit costs, increases Compliance culture, and manages Risk.
eTHIC ensures you remain abreast of evolving procedures and regulatory guidelines as your organization grows and regulations evolve. Our offerings encompass comprehensive GRC (Governance, Risk, and Compliance) solutions complemented by top-tier professional services.
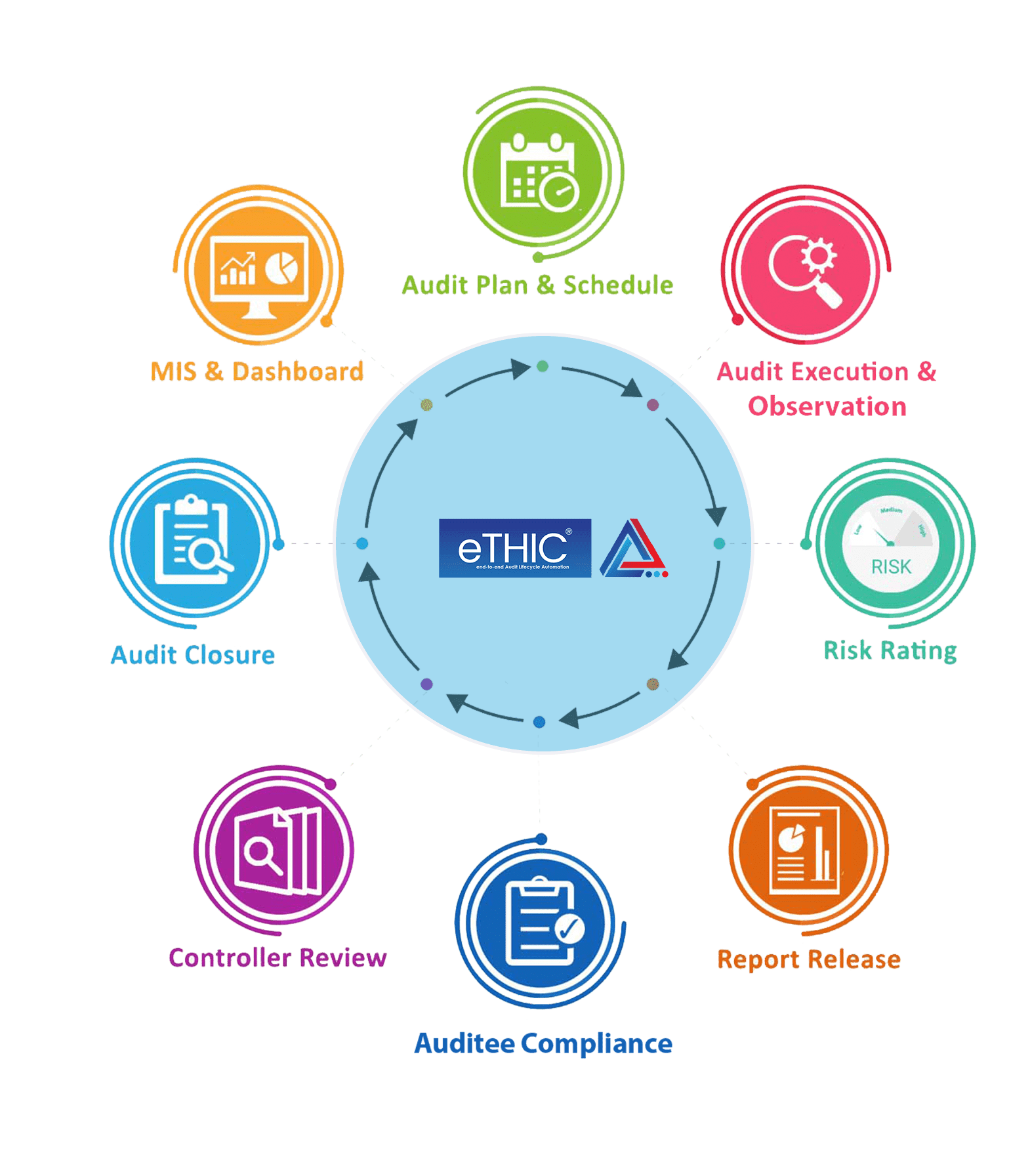
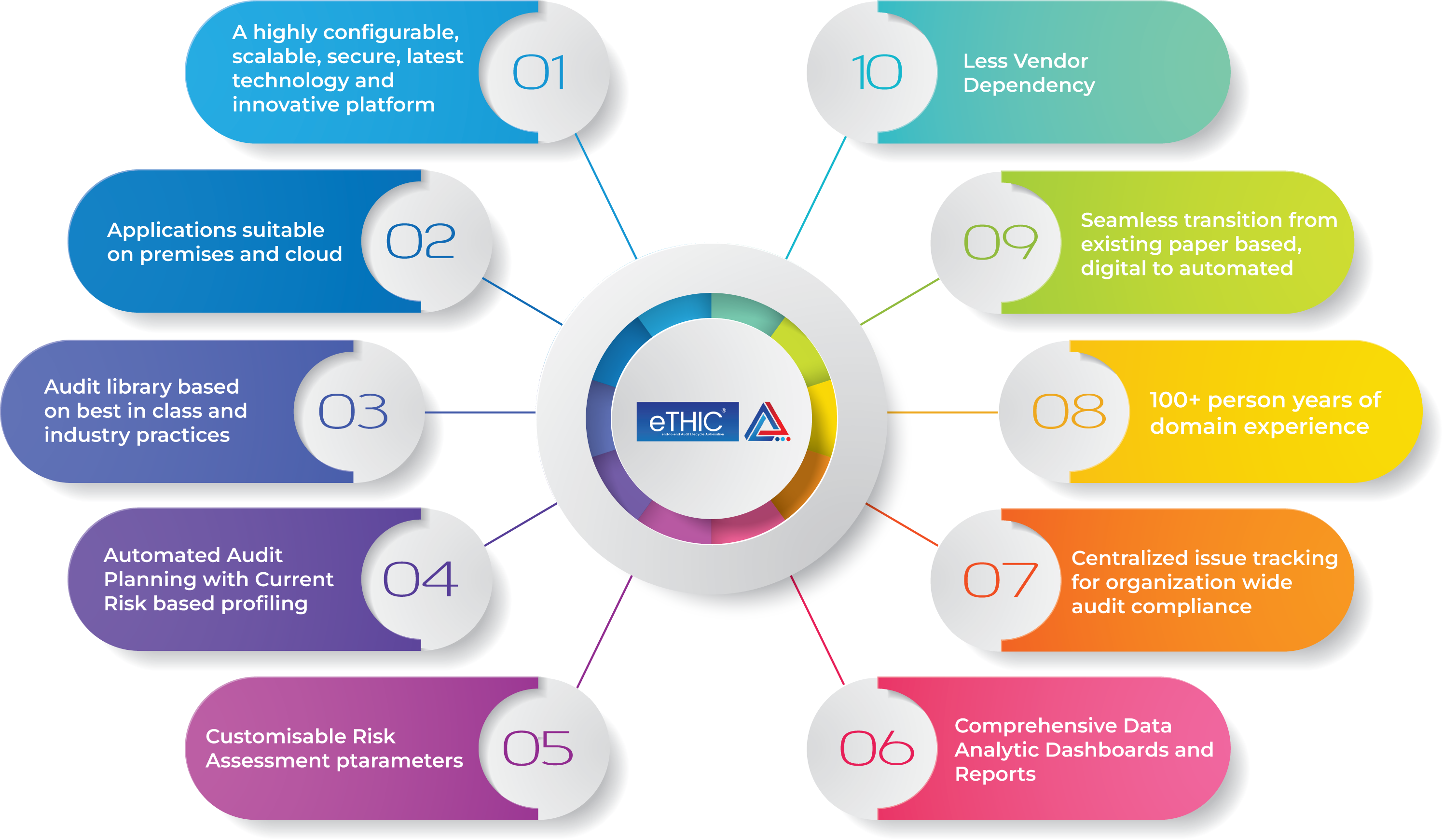
As the most comprehensive integrated solution on the market, eTHIC, a modular platform, caters to all your GRC requirements and can be customized for specific needs, such as Internal Audit and inspection.
eTHIC is a server-agnostic platform boasting enhanced management reporting, efficient monitoring capabilities, and streamlined data collection, all geared towards optimising your GRC framework.
eTHIC is a cutting-edge solution designed to provide a breakthrough in your digital experience. With robust features and unparalleled benefits, eTHIC is crafted to enhance efficiency, streamline processes, and elevate overall productivity.
Invest in eTHIC today and transform the way you work, unlocking a new era of productivity and success for your business.

We at NCS believe in the power of collaboration and collective creativity. That's why we've embraced the concept of co-creation, a dynamic process that involves bringing together diverse perspectives to shape innovative solutions.
It's about breaking down barriers and inviting you – our valued visitors, customers, and partners – to be a part of our creative journey. Join us on this exciting co-creation adventure. Together, let's turn ideas into reality and shape a meaningful and innovative future.
We understand that navigating the complexities of today's business landscape requires more than expertise - it demands strategic vision, adaptability, and a partner committed to your success. To make your internal Audits Transparent, Governance Risk-Aligned, and Compliance Efficient, and to create a seamless Digitized Auditing process, we bring together industry knowledge, innovative solutions, and a client-centric approach to drive your business forward. Expert guidance makes your Audit Risk process more futuristic and Agile. Contact our knowledge staff on how we can help you begin or refine your experience.

Moved on from our Product





You're well aware of the current situation in the�Indian stock markets�investors are understandably worried as their past gains have been wiped out in a matter of days. However, despite this volatility, we must not lose sight of a fundamental truth:�market fluctuations are inherent and inevitable.
Paddy's Corner


At NCS, impactful learning sessions are fueling a new wave of professional growth and bold thinking across teams. Covering essential topics such as Banking & Fundamentals, Innovation, Creativity, and Project Management, these sessions are designed to inspire associates to think bigger, act smarter, and continuously upskill in a dynamic business environment.
NCS'ites Speaks

Let's explore the concept of delayed gratification and why those who master this quality are more likely to succeed
Paddy's Corner

eTHIC Platform is the unrivaled No.1 Audit Software in the subcontinent. This accolade is a testament to our commitment to innovation, unparalleled functionality, and the trust bestowed upon us by our valued clients.
Audit software plays a crucial role in modern business environments for various reasons. Audit software is a valuable tool that contributes to the effectiveness, efficiency, and reliability of audit processes, ultimately supporting organizational governance, risk management, and compliance objectives.
Audit software contributes to risk reduction in various ways by providing organizations with tools and features that help identify, assess, and mitigate risks effectively. Audit software plays a vital role in reducing risk by providing organizations with the tools and insights needed to identify, assess, and manage risks in a proactive and systematic manner.
Yes, having a transaction monitoring system is considered essential for various industries and sectors for several reasons. Transaction monitoring refers to the process of tracking, reviewing, and analyzing financial transactions to detect and prevent potential risks, fraud, or illegal activities.
Audit tools play a crucial role in helping businesses maintain transparency, ensure compliance, manage risks, and improve overall operational efficiency.
Audit software is suitable for all industry and specifically for insurance sector, offering tools and features that support compliance, fraud prevention, risk management, and overall operational efficiency. It helps insurance companies navigate the complex landscape of regulations and risks while maintaining accuracy and transparency in their operations.

Designed and Developed by NCS
